Another post by your roving correspondent, Brian of London.
Yesterday afternoon I attended the International Institute for Counter-Terrorism (ICT)’s International Conference on Cyber Terrorism at the IDC Herzliya.
I’m sure there will be some full write-ups in the press but I’ll share a couple of snippets here. A speaker who was working on the Israeli Government’s e-Gov program told some stories connected with the constant attacks the Israeli Government websites are under. As he said “We’re the Government, we’re Israel and we’re the Israeli Government”.
All the networks of the Israeli Government are the most highly attacked networks on the planet.
During operation Cast Lead the government networks experienced peaks of 16,000,000 incoming connections per second. That is completely beyond the capability of any network switching equipment today. At least three attacks of this scale succeeded in taking down the government sites for periods of up to 20 minutes.
But I want to tell you what I did in the audience. The IDC has free open WiFi. Great you say, I can check my Facebook when things get dull. Open WiFi is when you don’t have to put in a password to get online: you just open your computer, attach to the access point and then often click some silly page to “accept” the terms.
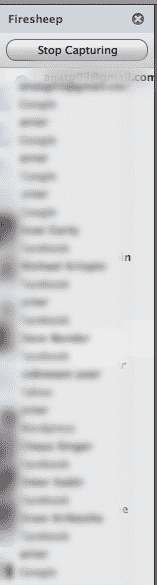
A few weeks ago a small program (actually an extension to the Firefox web browser) called FireSheep was released. It makes it very easy to do something which had always been possible on open WiFi if a little difficult.
When you run FireSheep and connect to an open WiFi spot it gives you a side bar. I’ve included a screen shot but blurred the names to protect those I could now be impersonating. As other people join the hot spot when they log into a long list of popular services like Facebook, Twitter, New York Times, Yahoo, Yelp, Gowalla, Foursquare etc. you see their name in your browser. If they log in to Facebook you even get a nice picture of them so you can look around the room or the coffee shop and spot them.
If you take it one stage further (the step I did not take last night) you double click on their picture and take over their session: you BECOME them on Facebook (or whatever site they’ve used). You can change their status, update their picture, maybe even make them a friend of Mahmoud Ahmadinejad.
For some reason this program has not received much attention in Israel where every coffee shop offers open WiFi. All these coffee shops would have to do to stop this is use a simple password known to all. Even a single digit “1” as a password would be enough to break FireSheep.
This is actually a bigger problem and the only real solution is for all these websites to switch to using a secure connection all the time (https:// instead of http://) and not only just for the log in as they do now. Gmail made this switch earlier this year and the team that did it have written technically that it doesn’t require an increase in hardware as modern servers can handle the https encryption so efficiently.
I tested at this conference on purpose: if the people attending that event are so vulnerable, how about you sipping your latte at the coffee shop?
Update: YNet has covered the same story: Firesheep ???? ??? ????????